It's the best Windows honeypot offering, full of features, and easy to set up.
What it does offer is tops in the industry.
Roger A. Grimes
Author, Honeypots for Windows. Apress
Enhanced intrusion and insider threat detection for your network
Honeypots have low false positives and easily complement other existing forms of security that may be in place.
Designed for use in a Windows based corporate network, it is easy to both deploy and maintain.
KFSensor is fully supported, and has been regularly improved during its 20 years of production use.
KFSensor acts as a honeypot, designed to attract and detect hackers and worms by simulating vulnerable system services and trojans.
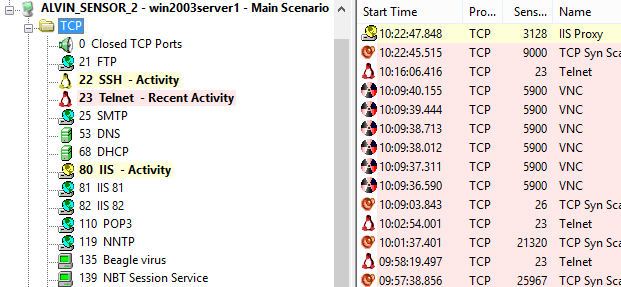
KFSensor is pre-configured to monitor all TCP and UDP ports, along with ICMP. It is also configured with the emulation of common services.
It starts monitoring right after its installation and can be easily customized to add additional customer services later on.
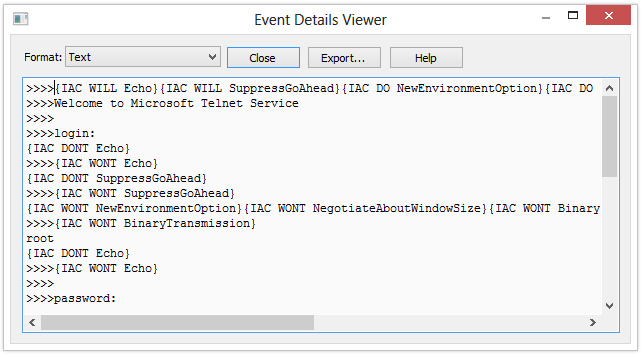
By responding with an emulation of a real service KFSensor is able to reveal the nature of an attack whilst maintaining total control and avoiding the risk of compromise.
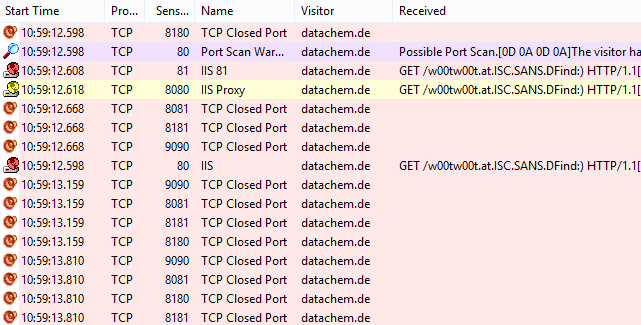
As well as individual service attacks KFSensor detects and responds to port scans and denial of service DOS attacks and prevents itself from being overloaded.
By responding with the emulation of a real service, KFSensor is able to reveal the nature of an attack, whilst also maintaining total control of the incident and avoiding the risk of compromise.
As well as individual service attacks, KFSensor also detects and responds to port scans and denial of service (DOS) attacks; and prevents itself from being overloaded.
KFSensor can send real time alerts by email or via integration with a SEIM system.
The KFSensor administration console allows events to be filtered and examined in detail, allowing comprehensive analysis of any attack.
KFSensor also makes a full packet dump available for additional analysis, using tools such as Wireshark.
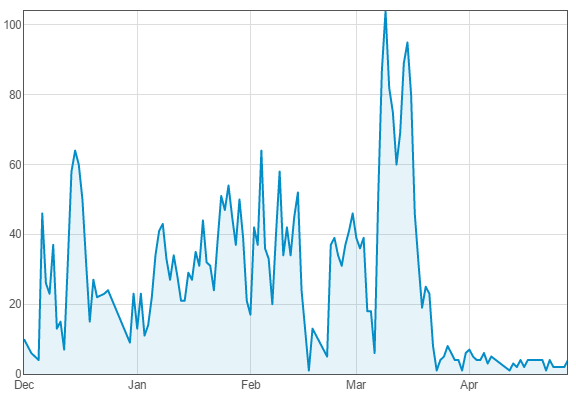
The KFSensor Reports module provides a range of reports and graphs that can be used to analyse many different aspects of the attacks facing an organization.
The reports are particularly useful in highlighting patterns of attacks that are only identifiable over time.
All reports can be filtered on a time period, attack type and the location of the visitors, allowing for detailed study and analysis of a particular threat.